Fatboy is a novel RaaS sample with a funny-sounding name. Fatboy is not the only name that can be used to refer to this ransomware: Dxh26wam and PyCL are the alternative ones to use. A complete package of this crypto-virus is promoted in the shady part of the Internet called the dark web. The authors of Fatboy virus describe their product as a profitable opportunity. At first, this service was suggested to Russian speaking users, but the ad for Fatboy was adjusted to English-speaking users as well.
Processes that are launched by Fatboy ransomware
Soon enough, the first cases of infections with Fatboy occurred and researchers got their hands of the payload, 399tbz21.exe or Dxh26wam.exe file. Even though the ransom note is almost identical to CTB-Locker, these variants are not the same.
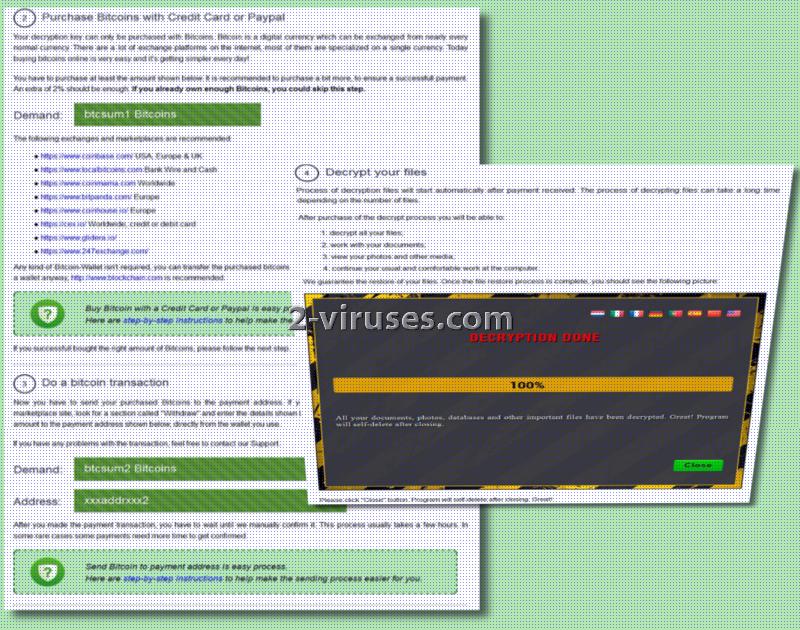
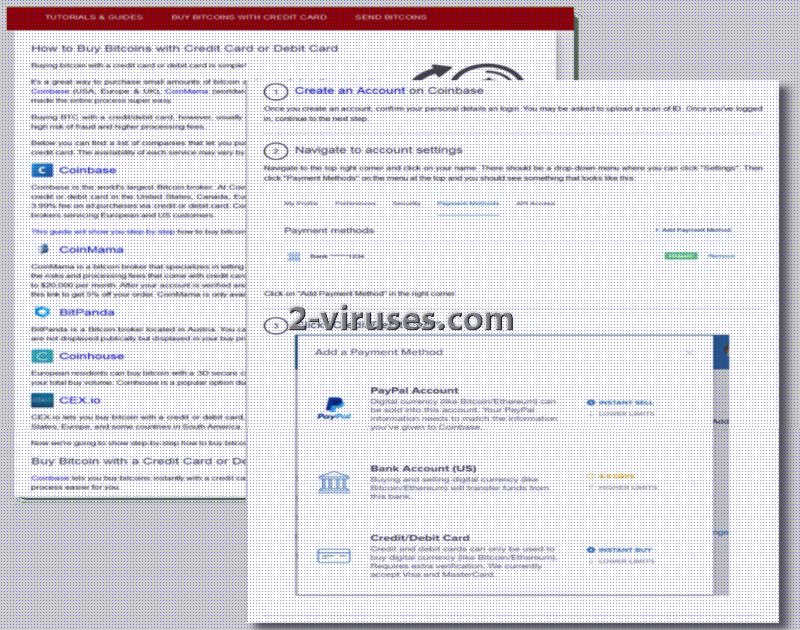
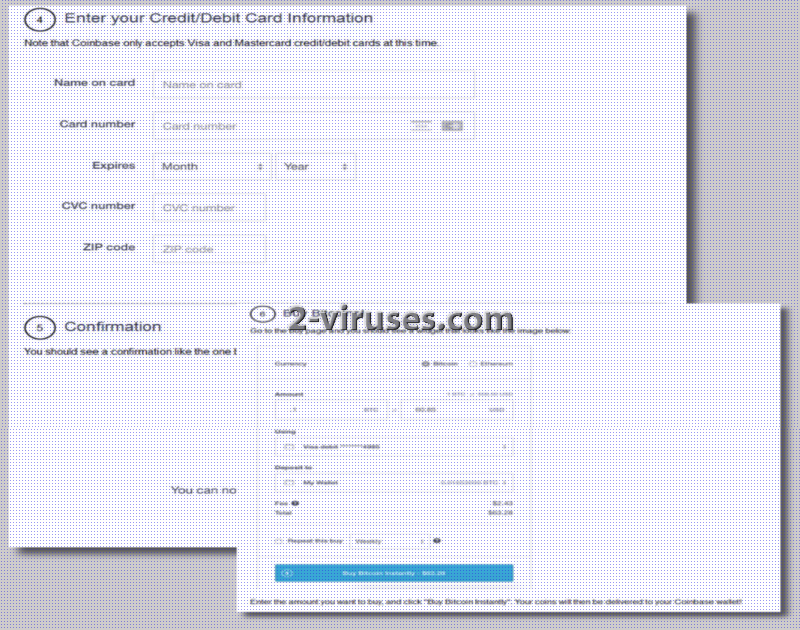
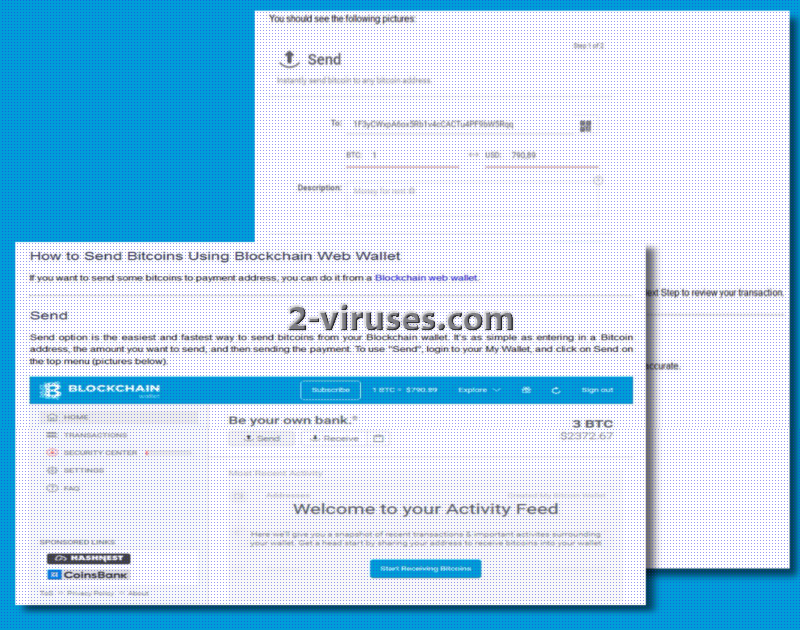
Additionally, Fatboy ransomware stands out of other infections in a way that it provides explicit instructions, tips and other information on how bitcoins are to be purchased and etc. Security researchers have identified that encryption by this sample is completed in Python and the graphical user interface is programmed in Delphi.
Fatboy ransomware could target people from all over the world as the ransom notes can be adjusted in a variety of languages. In English, Chinese, Spanish, Portuguese, German, French, Italian, Netherlandish languages are the eight possible ways that the ransom note can be presented.
In order to review these instructions, users are to launch How Decrypt My Files.lnk which will lead to the .html files. This variant encodes files with AES-256 and then, applies RSA-2048 to cipher the decryption key. Executables that are not usable all start featuring .crypted extension.
Fatboy virus is promoted as a C++ sample and functions on Windows operating systems x86/x64. Five hundred different file types can be encrypted. For different victims, the demanded ransom might differ. Why? This variant derives the appropriate fee from the victims’ IP addresses. Fatboy evaluates the amount that people from a specific country are capable of paying.
The amount that are presumably to be demanded fluctuates between 0.2 to 0.3 BTC (approximately from 331.50 to 497.25 US dollars). Hackers that are responsible for Fatboy could be from Uruguay as the payload could contact a C&C server which has an IP, indicating this country. Security researchers have also designed a demonstration of the Fatboy ransomware attack. You can see it here:
Good news for victims of Fatboy ransomware victims
Free decryption of files that have been ruined appears to be plausible. Security researcher Michael Gillespie has indicated that victims should contact him as there is a chance that he will be able to assist them in the file-recovery process. No matter the circumstances, users should never provide hackers with money that they do not deserve. By making bitcoin transactions to these crooks, you would only support ransomware project just like this. Raising profits for crooks only encourages hackers to continue on producing crypto-viruses. Since there is a chance that Gillespie can help you recover data, we advise you to do so.
However, we should also distinguish several techniques that can protect files from encryption. Instead of having your files only in their computer hard drives, users should have multiple locations from which data can be retrieved. Online backup storages have become a popular service to exploit. On the other hand, you could store files in USB flash drives. Both of these options are beneficial for the user.
Distribution of Fatboy ransomware
Fatboy ransomware as a service is promoted on the dark web. Random people can become involved with this variant and decide on the way it should be transmitted. One of the possible methods is that crooks will distribute their product via malicious spam letters or take advantage of exploit kits. Be careful when it comes to opening random email messages in your inbox. It is possible that random people will be targeted. Additionally, do not download applications or single files from unreliable file-distributing services.
Spyhunter or Plumbytes are very convenient tools that will help you get rid of this ransomware. Fatboy virus could be eliminated manually, but it might be dangerous to do so since removal of ransomware requires certain knowledge and skills. Read more about it in the section below.
Fatboy Ransomware quicklinks
- Processes that are launched by Fatboy ransomware
- Good news for victims of Fatboy ransomware victims
- Distribution of Fatboy ransomware
- Automatic Malware removal tools
- How to recover Fatboy ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Fatboy ransomware encrypted files

Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Fatboy ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Dxh26wam ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of PyCL ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Fatboy ransomware. You can check other tools here.Step 3. Restore Dxh26wam ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually PyCL ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Fatboy ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.