EvilLock crypto-virus has a certain style: it encrypts files and uses this as a leverage to demand for money as a ransom for file-recovery. Sadly, this tactic has gained the leading position in malware viruses, meaning that ransomware samples are turning into the most successful scams to profit from. EvilLock variant is not an old variant since it has been detected just this week. For now, victims cannot be cheered up with a free file-recovery tool, but security experts are putting their resources and efforts into producing such programs and making files accessible again. However, this process requires time and research: for this reason, victims are have to stay still and try not to choose the easy way out: to simply pay the demanded ransom. EvilLock crypto virus has selected to encode files with AES encryption algorithm, which will turn all of your files completely useless. Only a certain time is going to be given for users to cope and send a transaction of bitcoins: only 3 days. Considering the pressure that a person might feel, it is presumable that some might not stand the heat and pay money to receive decryption software. This variant received its name after the extension it appends to the corrupted data: .evillock.
Is EvilLock virus just as evil as it implies to be?
Yes, every ransomware infection is evil. This variant simply desires to emphasize two things: it is evil and it locks stuff. EvilLock virus gains access to your device, inserts its payload into a random folder and starts its detrimental activity. AES algorithm is selected as the weapon against your files, shooting holes into them and making them completely powerless. After the process of encryption is concluded, every file which was determined to be fit for encryption gets a stamp: .evillock extension. However, this is one of the last stages of a ransomware infection: before you will notice that files have been modified, EvilLock virus is going to have to be successful in a couple of other procedures. It has to make an effort to come into contact with its C&C server which is controlled by hackers that designed this ransomware.
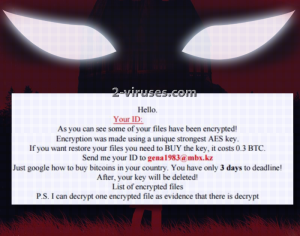
Infection is programmed to disclose information about a new victim and share various information about him or her. Before that, malware will slip entries into Windows Registry: it desires to be launched automatically with the rest of software applications. Every victim also gets a unique ID number which helps hackers determine which victim has paid the ransom and those people that have not. [email protected] is the email address that victims can contact, but we highly doubt that anything positive could come out of a conversation with hackers. They are only interested in receiving 0.3 BTC which equals exactly 303.33 US dollars. Ransomware will also change victims’ desktop image and append the ransom note in html and txt files. HOW_TO_DECRYPT_YOUR_FILES.TXT and HOW_TO_DECRYPT_YOUR_FILES.HTML are going to open up and introduce you to the demands that hackers are instructing you to follow.
Finding a solution to the encrypted files and reviving them: EvilLock virus edition
EvilLock virus has just recently been detected as a malware threat, for this reason, there is no decryption tool available. For the time being, that is. We have no doubt that if enough research is put, a free decryption tool is going to be released. Storing your valuable system in your hard drive and not placing them in another secure location is extremely dangerous, especially considering that ransomware viruses have become so popular among hackers. New variants get released everyday: for this reason, please secure your data by keeping it in multiple places. As for the files that have already suffered from encryption, you can try to retrieve your files via Shadow Volume Copies or universal file-recovery tools. You can find more info about this in the last section of our article.
What are your options after you get infected with EvilLock virus? How did it happen, exactly?
We have reason to believe that EvilLock virus spreads just like other ransomware infections. It can take advantage of exploit kits and thanks to them, enter a device unnoticed. For this reason, security researchers emphasize the importance of staying away from unreliable, vulnerable websites. Additionally, an odd email letter that ends up in your inbox should be treated with a high degree of suspicion. Do not open them immediately or download attachments that are found inside. Always pre-check if there are no warning signs, implying that this letter might be a part of malicious spam campaign. Bad spelling, bizarre email addresses are dead-giveaways. Switching to the topic of removal of EvilLock ransomware, we recommend that you use an anti-malware tool to secure your system and get rid of this infection. Spyhunter or Hitman won’t disappoint you. As we have mentioned, details about manual removal/decryption are uploaded below.
Evillock Virus quicklinks
- Is EvilLock virus just as evil as it implies to be?
- Finding a solution to the encrypted files and reviving them: EvilLock virus edition
- What are your options after you get infected with EvilLock virus? How did it happen, exactly?
- Automatic Malware removal tools
- How to recover EvilLock virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover EvilLock virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover EvilLock virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before EvilLock ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of EvilLock virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to EvilLock ransomware. You can check other tools here.Step 3. Restore EvilLock virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually EvilLock ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover EvilLock virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








