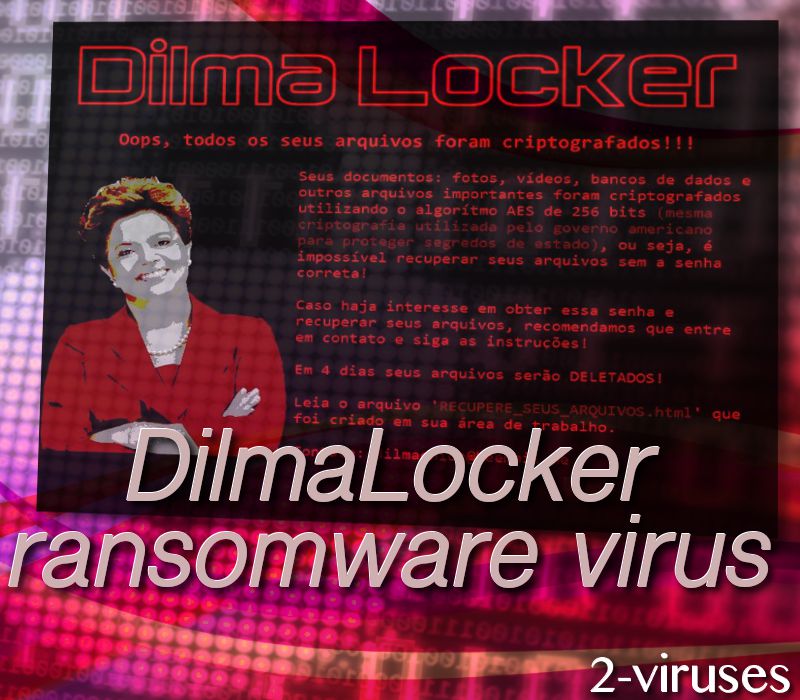
DilmaLocker ransomware virus is a Brazilian malware sample. We have already observed a few ransomware infections that are targeting Brazilian people: TeamXRat is one of them. The newest sample appends an original extension of .__dilmaV1 to the encoded digital data. RECUPERE_SEUS_ARQUIVOS.html file serves as a ransom note and provides hackers’ demands in the Portuguese language. Ironically, this crypto-virus is named after a politician Dilma Wana Roussef. She was the 36th President of Brazil who ended up receiving high disapproval ratings from Brazilian people, and was a reason for many protests. This is not the first time when ransomware was named controversially: Jew Crypt and TrumpLocker are one of the examples.
DilmaLocker computer virus encrypts files and targets Portuguese-speaking users
DilmaLocker crypto-virus is a disturbing infection as it will use AES-256 cipher to encode files. This algorithm is also applied by infections like ABCLocker and Fake WindowsUpdater. Afterwards, ransom notes and notifications from DilmaLocker virus are going to start appearing. The ransomware is supposed to serve a screen-locker, featuring a photo of Dilma Roussef and instructions from hackers. This locker will urge users to read the .html file and contact [email protected] email address.
In a page that will launch in your preferred browsers, users will be informed that the only way to pay the ransom is to send R$3000,00 Brazilian Reals. This currency was also demanded by authors of PayDay. The amount equals approximately 968.05 USD. While hackers claim that victims can negotiate, they give only 4 days for the payment to be sent. If this task is not completed during this time period, hackers will no longer be able to decrypt files.
According to the technical analysis (VirusTotal), there are multiple strategies that the payload of DilmaLocker ransomware can use to disguise itself. First of all, it can attempt to be a file of Adobe Acrobat Reader DC and be distributed as an AdobeRd32.exe executable. However, it can also be posing as a CV resume Alex-Barbosa—curriculo-vitae-2017.pdf.exe. Both of these payloads are expected to be transmitted via malspam that urges people to voluntarily download malware samples. However, the strategy of sending fake resumes has been noticed before in PEC 2017 ransomware sample.
Much to our surprise, we did not find any mentions that the ransom should be sent via bitcoin payment system. Nevertheless, after victims contact hackers via the indicated email address, they could be required to make a donation of 0.208632 BTC. However, paying fees for decryption does not mean that any of encoded data will be restored. Crooks could be playing their victims and have no intention of helping them. After fees are paid, crooks could disappear and leave users hanging (StorageCraft).
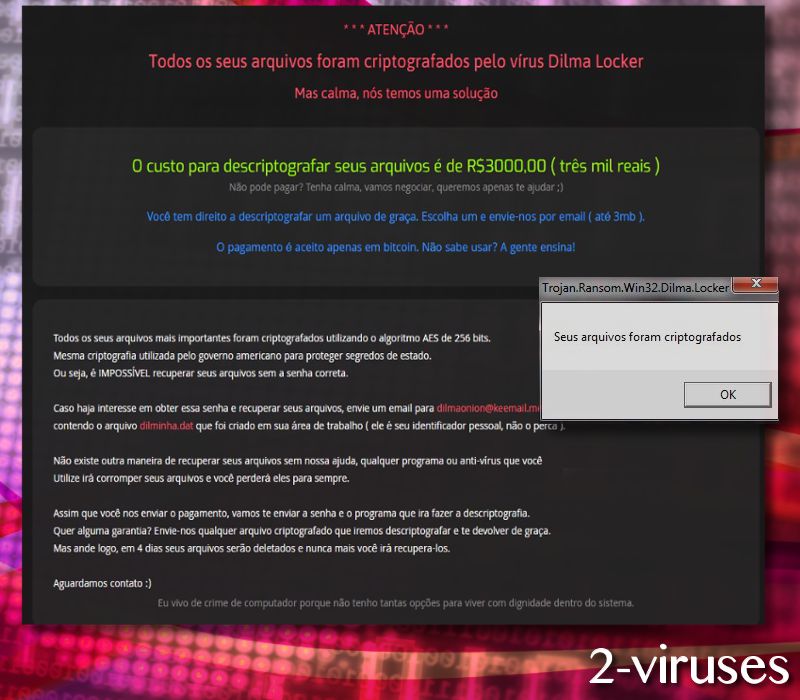
According to the messages that are displayed by DilmaLocker crypto-virus, people will be offered a chance to decrypt a few of their files. However, their size is restricted to be smaller than 3MB. This is an opportunity that usually should be exploited. Victims are recommended to send encoded executables to hackers and wait for them to decrypt them. As soon as the restored versions are received, people should not hesitate to provide them to security researchers. This could help experts generate a free file-decryptor. However, sending requested ransoms is never a good idea. People should never allow extortionists to steal their money.
File decryption, removal and prevention of ransomware viruses
Ransomware viruses are one of the most awful infections around. Unfortunately, the number of variants is gradually increasing and security experts calculate that even more of them are going to be introduced. Therefore, we hope you will store your files in backup storages. This can save you from all of the trouble of trying to recover files when a ransomware virus strikes. More about these options can be found below. Additionally, we hope that you will be cautious when responding to email letters from unknown senders. Never download random attachments or follow URL’s. For a proper protection for malware (and removal of ransomware), we insist you try Spyhunter security tool.
Dilmalocker Ransomware Virus quicklinks
- DilmaLocker computer virus encrypts files and targets Portuguese-speaking users
- File decryption, removal and prevention of ransomware viruses
- Automatic Malware removal tools
- How to recover DilmaLocker ransomware virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover DilmaLocker ransomware virus encrypted files

Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover DilmaLocker ransomware virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before DilmaLocker ransomware virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of DilmaLocker ransomware virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to DilmaLocker ransomware virus. You can check other tools here.Step 3. Restore DilmaLocker ransomware virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually DilmaLocker ransomware virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover DilmaLocker ransomware virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








