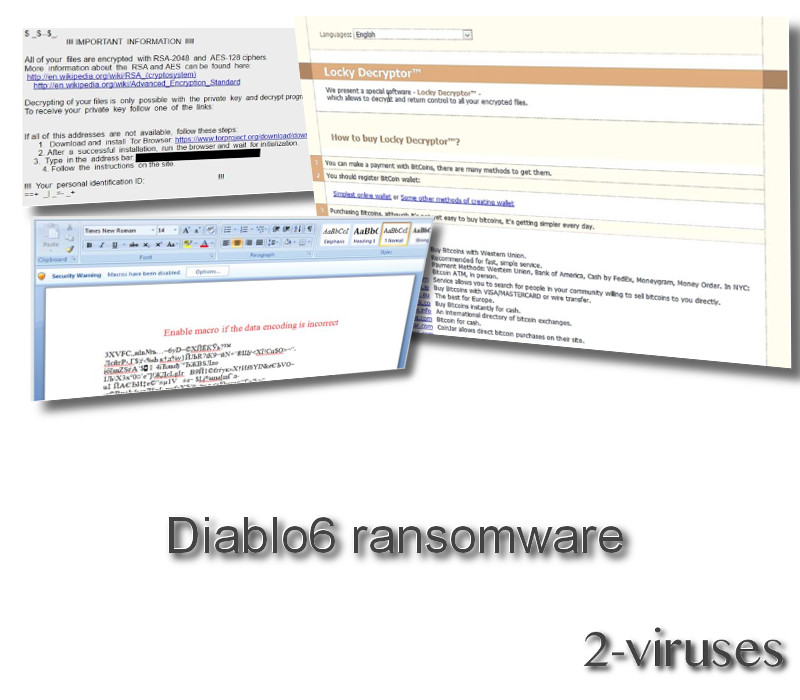
Do you remember infamous Locky ransomware? Well, it seems like this infections has resurrected in slightly different form and completely different name – please welcome Diablo6 ransomware virus. This virus uses the same cryptographies as Locky Ransomware – RSA-2048 and/or AES-128. Those are pretty strong cryptographies that can completely lock your files – it can be a real struggle to decrypt them later on.
Soon after being introduced, Diablo6 was replaced or, in other words, accompanied by a new Locky version: Lukitus crypto-virus (Locky ransomware’s two new variants Diablo6 and Lukitus get a boost from Necurs botnet. Ibtimes.co.uk). Both of the variants exploit strategies of delivering malicious spam campaigns that contain detrimental archives, concealing JS files. In addition to this, their malspams are strongly-supported by Necurs botnet. If malicious attachments are implanted into devices, they VBS Downloader scripts will be ran.
The ransomware is one of the most dangerous types of viruses – they attack users all around the world, encrypt most of the files stored on the computer and then ask for the ransom to be paid in order to receive the decrypter and retrieve those locked files. It’s always the best to hear the experience of the victim itself. User 1dunn00 described his experience with this ransomware in a post on Reddit:
Hello, I believe I have a virus on my computer. It changed the wallpaper and dropped several files. All of my files were renamed, like:
DB2B3823-2F3823932-3292.diablo6
and when i right-click and select properties, it says DIABLO6 File. Just for the record I do not play Diablo game… it looks like a virus. When I open the readme file, I get a page that says “Locky Decryptor” on it and it is in brown color. The page asks me to pay 0.5 BTC to get my files back. Help, pls..
It is an actual description of Diablo6 ransomware attack (1).
Processes of Diablo6 virus
Back in the day Locky ransomware was considered to be one of the deadliest and wide spread ransomware viruses. Now it’s back in a new form and as confirmed by cyber security researcher Racco42 (2), now it comes by the name of Diablo6 ransomware and is mostly distributed via spam emails. In case you are interested, you can also take a look at the files of this infection at Pastebin (3).
So it is clear that this infection comes as an attachment to the email from spam category. All it needs you to do is to open that attachment and all of files will be automatically placed on your computer, malicious processes started. Firstly, Diablo6 virus will run a scan of your system and detect files that can be encrypted. Basically, all of the most common file types fall into this category. Full list:
.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt
After the encryption, extension .diablo6 will be added to every one of your files and they will be encrypted with RSA-2048 or AES-128 cryptography. From now on, you will not be able to open those files. Immediately after that, you will notice 3 new files placed on your desktop – Diablo6.html, Diablo6_[4_digit_number].html, Diablo6.bmp . Your desktop wallpaper will be also changed automatically.
This is the original message displayed by Diablo6 ransomware, also known as the ransom note:
IMPORTANT INFORMATION !!!!
All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about the RSA and AES can be found here:
hxxps://en.wikipedia.org/wiki/RSA_(cryptosystem)
hxxps://en.wikipedia.org/wiki/Advanced_Encryption_StandardDecrypting of your files is only possible with the private key and decrypt program, which is on our secret server.
To receive your private key follow one of the links:If all of this addresses are not available, follow these steps:
1. Download and install Tor Browser: hxxps://www.torproject.org/download/download-easy.html
2. After a successful installation, run the browser and wait for initialization.
3. Type in the address bar:
4. Follow the instructions on the site.
!!! Your personal identification ID:
As you can see, victim is informed that the files are encrypted and in order to fix this problem, Locky Decryptor needs to be purchased. At the time, it costs half of a bitcoin, which converts into around sixteen hundreds of dollars. It can be purchased on the deep web, using TOR web browser and visiting links promoted on the ransom note.
Unluckily, there is no way to decrypt Locky encryption for free, and the same goes to the Diablo6. The only hope in this situation is to either use Shadow Volume Copies or system backup to restore your computer into the state previous to the virus. It is also a good idea to get a real-time protection which would deny malware trying to get into your computer. We recommend to use Spyhunter or any other reputable tool of your choice which features real-time protection.
Diablo6 Ransomware quicklinks
- Processes of Diablo6 virus
- Automatic Malware removal tools
- How to recover Diablo6 ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Diablo6 ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Diablo6 ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Diablo Virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Locky
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Diablo6 ransomware. You can check other tools here.Step 3. Restore Diablo Virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Locky tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Diablo6 ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.

References:







