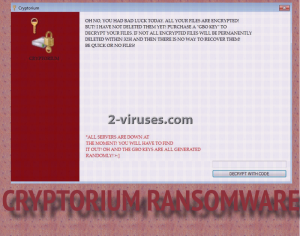
Say hello to Cryptorium: a new ransomware infection that encrypts files and demands victims to purchase a GBO key for decryption. This specific example does not exactly possess any extremely innovative techniques that would be directed against infected users, but it is a threat to the cyber world and people have to be informed about it. If this is the first time you see the term “ransomware”, it is a virus that exploits powerful algorithms for encryption of files and requires a solid amount of money to return the infected files back to normal. Cryptorium virus not only ruins data with a strong cipher, but also indicates to delete this data within 32hours. If we take these allegations seriously, a permanent loss of files is a possible consequence of the Cryptorium virus.
Cryptorium: what, where and why? Why was it created?
There are a couple objectives that ransomware viruses have to successfully execute before their plans for encryption can take place. After the payload lands in your system, it will initiate some modifications that will be directed to Windows Registry Keys. Some keys’ main function is launch and load programs automatically. Cryptorium virus hopes to insert its payload to the list. After that, the payload gets automatically launched and has no problem in running scans or contacting the hackers C&C to inform them about a new victim. The exact types of files that the ransomware targets are unknown, but there is enough evidence to suggest that the most prevalent types of data can be transformed into inaccessible icons. Potential victims of this virus can be Russian or English-speaking users as reports imply that the ransom note can be displayed into both languages. Since is a rather new version of ransomware, it is difficult to draw an extremely detailed description. There are no claims about an extension to the encrypted data or whether this infection is related with any other sample of ransomware. You can get acquainted with the ransom note (both in english and Russian), by reading the texts below. If you happen to receive this note on your screen, please contact us or other reliable security technicians.
In the episode of Cryptorium virus and its travels
Cryptorium virus might be skulking in your email inboxes that usually feature a lot of misleading letters. Hackers are fond of starting campaigns of infectious emails that get transmitted to various recipients. The messages usually contain extremely hot topics that require attention as soon as possible. If you receive a very intriguing letter from your bank or other authority that you are a client of, always make sure that the senders’ email is identical to the one that is indicated as official. Due to various vulnerabilities, hackers can easily upload malicious scripts into files (executables are usually appended to the infectious letters). As we have promised, we are going to give you some recommendations for the future. Firstly, you are to be more cautious when it comes to your emails. Clean your inboxes from spam regularly.
Cryptorium, decryption and aspects that are related with the retrieval of data
Cryptorium is a complicated new variant and security researchers are going to have to dig deep to find a solution. Until then, do not fall on your knees and beg for forgiveness: hackers are completely immune to begging. We have high-hopes about IT technicians generating free codes for decryption of files. On another note, you should remember that if you store your files or keep copies of them in secure flash drives, you are protected from ransomware. Since they cannont threaten you with a permanent loss of your files, you won’t be tricked into paying solid amounts of money to the hackers. Specific number of demanded bitcoins is not yet determined. However, we assume that the sum can fluctuate from 0.2 to 3 BTC.
Spyhunter or Malwarebytes is here to inform you about the state of your device and give you the best protection from malware infections. By regularly running scans and keeping your software up-to-date, you are reducing the risk of getting infected with Cryptorium virus. If you are desperate to find a solution for his infection, the earlier listed programs are going to help you to fix this issue. Manual removal of ransomware viruses can be implemented with our constructed guidelines. For information about universal decryption possibilities, scroll down as well.
Cryptorium Ransomware quicklinks
- Cryptorium: what, where and why? Why was it created?
- In the episode of Cryptorium virus and its travels
- Cryptorium, decryption and aspects that are related with the retrieval of data
- Automatic Malware removal tools
- How to recover Cryptorium ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Cryptorium ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Cryptorium ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Cryptorium ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Cryptorium ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Cryptorium ransomware . You can check other tools here.Step 3. Restore Cryptorium ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Cryptorium ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Cryptorium ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








