CHIP crypto-ransomware has been identified with this name due to the extension that it gives to the encrypted data: .CHIP. RIG-E (Empire) Exploit Kit has been spotted to be exploited as a tool to poke security holes and spread malware. Exploit kits are applied on various web servers: their primary goal is to investigate visitors’ devices and reveal the vulnerabilities that could be selected for a smooth invasion. In this case, if a person visits a domain that has been influenced by a RIG-E Exploit Kit, then the codes can aim to proceed with their duty of finding insecurities. If the search ends with positive results, then a malicious executable can be placed into the affected device. This “malicious executable” can turn out to be a payload of a ransomware. For this reason, visiting random domains is definitely not a recommended activity.
About CHIP Virus
There are more tricky aspects about CHIP virus. For example, it encrypts files with AES, and this key is going to get encoded with RSA-512 cipher for maximum security. Besides that, many of features of this variant are quite common to ransomware viruses. For instance, even though this ransomware has been identified to spread in a specific way, its actions after arrival are not going to be so different from the ones performed by older models.
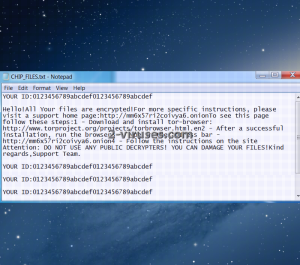
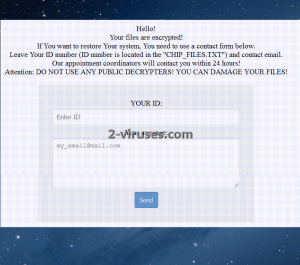
The payload of CHIP ransomware will not aim for the stars: one of the objectives is to interfere with Windows Registry Keys. This meddling is executed in order to add the payload of CHIP virus to the list of executables that are regularly and automatically ran. Since the vile executable will obtain the luxury of being active without victims’ knowledge, it will have the chance of secretively encrypting all of your files. After ransomware will put the finishing touches on the encryption process, it will begin to pursue another instrumental aim. It will try to convince people that paying money for decryption is the smartest choice. It will drop CHIP_FILES.txt file which will contain the most general information. It will contain ID numbers of victims and encouragements to download TOR browser in order to access the provided website. After users access the recommended domain, they will notice that they are urged to contact the creators of CHIP ransomware. It is presumable that, if the victims actually carry this action, they will be provided with the amount of ransom and the Bitcoin address to send the money, as well as the following contact e-mails: [email protected], [email protected], [email protected] and [email protected].
How is CHIP Virus Distributed?
We have already paid close attention to the methods that are selected for the distribution of CHIP ransomware. It will take advantage of exploit kits and attempt to infect insecure devices. If you are frightened by these viruses, you should never visit domains that are providing some sort of unreliable services. In addition to that, it was first assumed that CHIP virus invaded devices in an alternative way. Many of these infections travel as attachments to bizarre email letters. It might be that you will receive a fake notification about your membership, taxes, tickers or other significant topic. As security researchers indicate, these letters might contain files that are recommended to be downloaded for more information. Nevertheless, the mentioned file can turn to be a payload of ransomware infection.
How to Decrypt Files Encrypted by CHIP Virus?
For now, there is no possible way of decrypting files with a free decryptor. Since CHIP virus proceeds with a complexed combination of AES and RSA, malware fighters will have to examine this variant in great detail. Even though the creators of this ransomware state that attemps to decrypt files with public decryptors might potentially harm your files, you should still give it a shot. Before doing that, you should make copies of the encrypted files and remove CHIP virus from your device. Then, you can proceed with the attempts of restoring your data. People that are reading this article simply for pure awareness should store their files in backup storages, USB flash drives.
Spyhunter or Malwarebytes are the three significantly efficient helpers that will do everything in their power to assist you in the removal of CHIP virus.
Update of the 10th of December, 2016. CHIP ransomware started using the Dale extension.
Chip Virus quicklinks
- About CHIP Virus
- How is CHIP Virus Distributed?
- How to Decrypt Files Encrypted by CHIP Virus?
- Automatic Malware removal tools
- How to recover CHIP virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover CHIP virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover CHIP virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before CHIP ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of CHIP virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to CHIP ransomware. You can check other tools here.Step 3. Restore CHIP virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually CHIP ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover CHIP virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.