Bud ransomware virus is one of the crypto-malware samples that came out in September of 2017. Even though recent infections like InfinityLock or BlackHat ransomware are not the best crypto-viruses we have investigated, but they do pose a threat to owners of computers. As you might have heard, 2017 has been an exceptional year for hackers as the generation of ransomware infections has reached impressive numbers (Must know ransomware statistics 2017). If you store a lot of information in your hard drive, then these infections could aim to ruin this digital data and demand ransom for its decryption. This newly-detected infection has been determined to append .bud extension to all data it encodes. The latter encryption process is done with AES cipher.
Additional information about Bud crypto-virus
Bud computer virus displays an original screen-locker which begins with an over-utilized phrase: “Ooops, your important files are encrypted!”. The ransom note does not give information about hackers could be contacted. In fact, it only explains that 500 euros are expected to be paid as the ransom. Naturally, hackers are demanding to send transactions in bitcoin payment system (Why do hackers want payments through bitcoins?). According to the current exchange rates, this sum of euros equals 0.15308 BTC. Furthermore, it is unusual for ransomware to demand ransoms in euros: Schwerer and CryptoJacky are one of the examples that require euros instead of dollars.
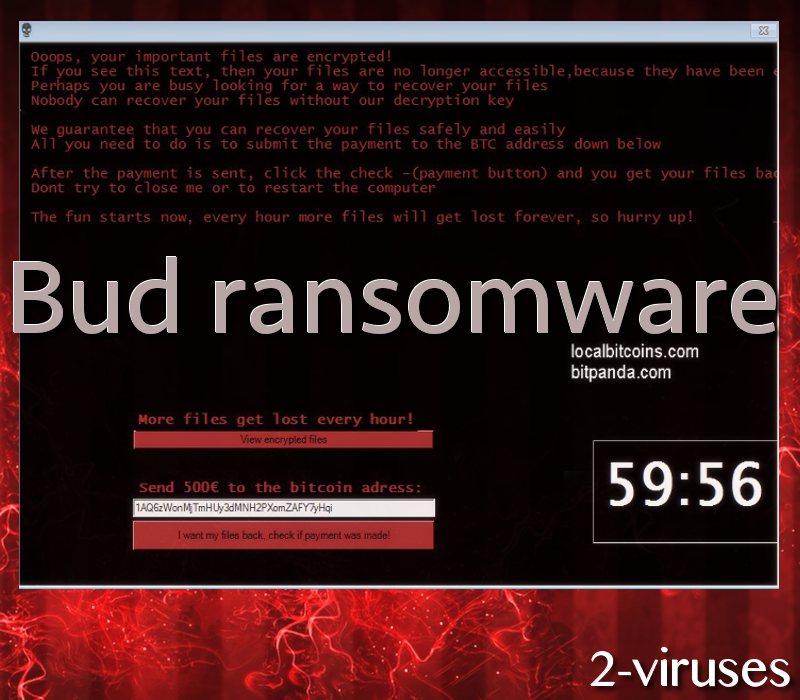
Once money sums are sent to hackers, victims are usually advised to contact hackers via email letters. Nevertheless, authors of Bud malware only provide a button “I want my files back, check if payment was made!”. Since the lock-screen will prevent users from accessing their desktops, people will be be able to see their encrypted files after clicking on “View encrypted files” button. The crypto-virus emphasizes that new files are going to be encrypted every hour. Victims are presumably going to be given a couple of days to send bitcoins to hackers, but we hope that people will have not pay the demanded fee (Ransomware attack: should you pay?).
The button which is supposed to fix files after ransom is paid might not even be functional. This means that even if you do buy bitcoins and generously provide them to hackers, your digital data could remain encrypted. Since hackers leave no contact information, you will have no way of contacting them and requesting explanations. Remember that hackers are vicious people and they have very little interest in helping users: all they care about is money.
Ransomware viruses: how should they be treated?
There is a proper method of treating ransomware infections. Security researchers stress out that ransoms should never be paid as they encourage hackers to continue on producing these viruses. More and more vicious people are getting involved in the ransomware industry. Now, thanks to ransomware services, people who do not have the skills to program a malware infection, can simply buy a virus off the Internet and distribute it for profit. We hope that none of our readers would be interested in participating in these cyber crimes.
One of the best ways to outwit hackers is to store your digital data in more than one location. For instance, hard drives could store your original files, but USD flash drives or backup storages can protect their copies. If you will have a respectable source to retrieve your files from, then there will be no reason to pay ransoms. Occasionally, special decryptors are created, but they do take time. There also is a possibility of restoring Shadow Volume Copies. However, most of the ransomware infections get rid of these copies. Read about the decryption possibilities at the end of this article.
Bud crypto-virus does not have a decrypter yet. However, we cannot neglect a possibility that researchers will introduce such a tool. Ransomware viruses can be distributed via email spam campaigns, malware-laden advertisements or websites, and even insecure RDPs. Please consider uploading files in a backup storages or find other ways to protect valuable digital data from encryption.
Bud Ransomware Virus quicklinks
- Additional information about Bud crypto-virus
- Ransomware viruses: how should they be treated?
- Automatic Malware removal tools
- How to recover Bud ransomware virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Bud ransomware virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Bud ransomware virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Bud ransomware virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Bud ransomware virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Bud ransomware virus. You can check other tools here.Step 3. Restore Bud ransomware virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Bud ransomware virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Bud ransomware virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








