aZaZeL ransomware virus is one of the newest samples of malware that has surfaced in the June of 2017. Security researchers found no relation between this variant and infections that came before it, which means that the authors of aZaZeL crypto-virus might be newbies in the field of producing ransomware infections.
However, the detected sample does utilize a familiar extension: .Encrypted, which is selected by other variants as well like Fake WindowsUpdater, GX40, LLTP, VapeLauncher viruses. Variant establishes different ID numbers for each victim so there would be no misunderstandings in recognizing which victim has paid the ransom. Hackers boss victims around and provides step-by-step guidelines that are supposed to lead to full-recovery of encrypted digital data.
Statement of results from examination of this crypto-virus
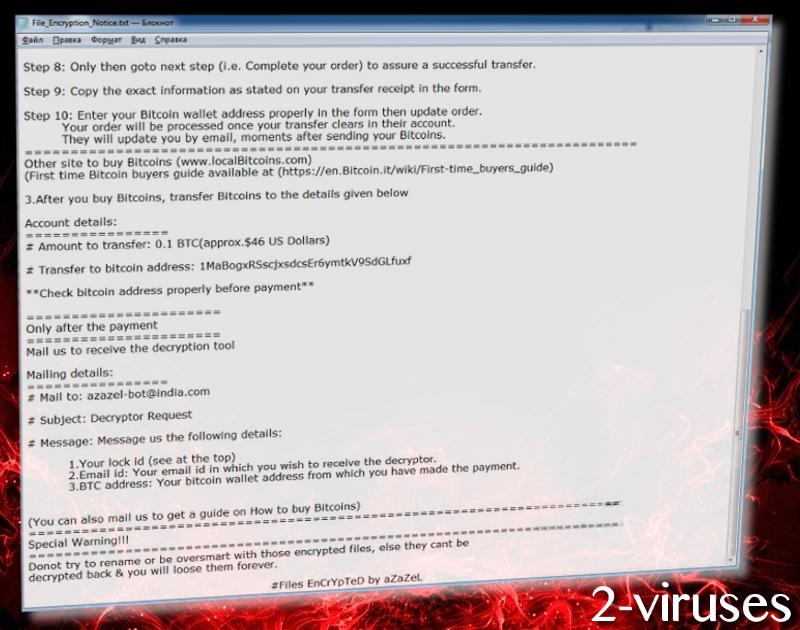
The exact cipher to be behind the encryption process is unknown, but it is either AES or RSA algorithms. To return files to their functional form, victims are supposed to pay 0.1 BTC which, according to the current rates, equals 268.19 US dollars. It is a terrible idea to purchase bitcoins and repeat every enumerated step. After bitcoins reach hackers’ bitcoin wallet, users are required to contact [email protected]. The message has to be structured according to certain requirements.
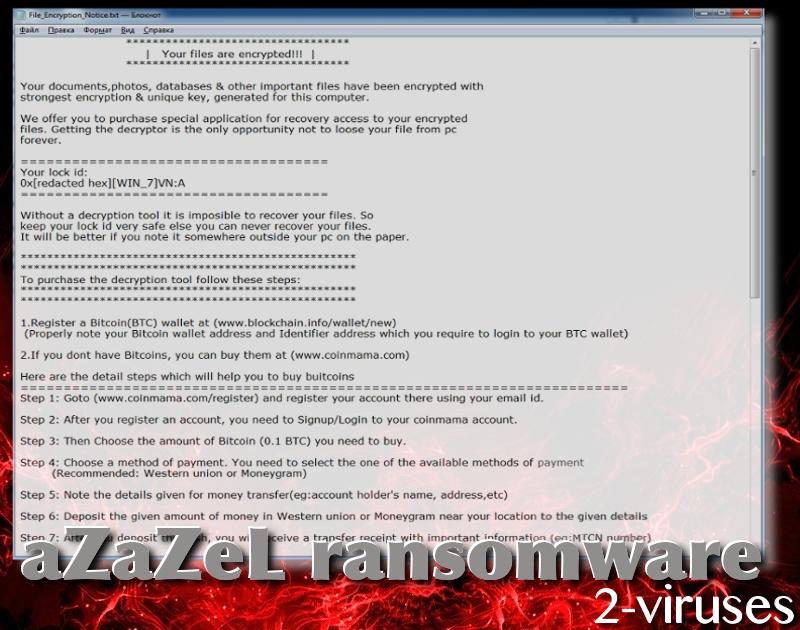
For instance, a subject of a message has to be “Decryptor Request” and the letter itself has to contain requested details. First of all, ID number has to be mentioned. It is found in the File_Encryption_Notice.txt file. Also, you have to specify which email address you wish to receive your decryptor. Lastly, victims have to include the address of their bitcoin wallet from which they made a transaction.
No matter how tempting it might be to pay the ransom, you have no guarantees that crooks will actually provide you with functional decryption key. There is a very good chance that they will simply disappear after obtaining 0.1 BTC and leave victims’ files inactive. Security researchers indeed can generate free-of-charge decryptors.
Therefore, we advise you to wait for such a tool to get published. On the other hand, you might have uploaded files into backup storages to have copies which you can retrieve anytime you wish. This decision will pay off when a ransomware is blackmailing you to pay a solid amount of money in exchange of your files. If you have a location to retrieve files from, they threats are meaningless.
Before you attempt to recover files, we have to warn you that some ransomware infections are programmed to re-encrypt files in case they are restored while the payload still remains in an operating system. This means that a malicious executable would be removed before file-recovery is pursued. You are welcome to follow the guidelines we have prepared for you, but removing ransomware is more difficult than other malware variants around. If you are more interested in an easier solution, we would advise you to run a full-security scan with an anti-malware tool like Spyhunter or Hitman.
The question of malware distribution is pretty clear in theory, but people might have some difficulties applying our recommendations to their browsing. Being cautious is the most important thing to do online as sneaky viruses can infiltrate because of an interaction with malicious content. Resist propositions to download software from unknown sources that might promote software apps that are modified/designed by hacker. In some cases, due to visitation to improper websites, a drive-by downloads brings malicious payloads.
Nevertheless, the most common technique for transmission when it comes to crypto-viruses is the technique of adding malicious attachments to seemingly-urgent letters that are sent from “legitimate” services. If someone contacts you about your flight tickets, bank account information, social security numbers, or simply offer you a chance to purchase good on sale, please check that the senders’ email would be clearly assigned to the actual service.
Azazel Virus quicklinks
- Statement of results from examination of this crypto-virus
- Automatic Malware removal tools
- How to recover aZaZeL virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover aZaZeL virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover aZaZeL virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before aZaZeL virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of aZaZeL virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to aZaZeL virus. You can check other tools here.Step 3. Restore aZaZeL virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually aZaZeL virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover aZaZeL virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








