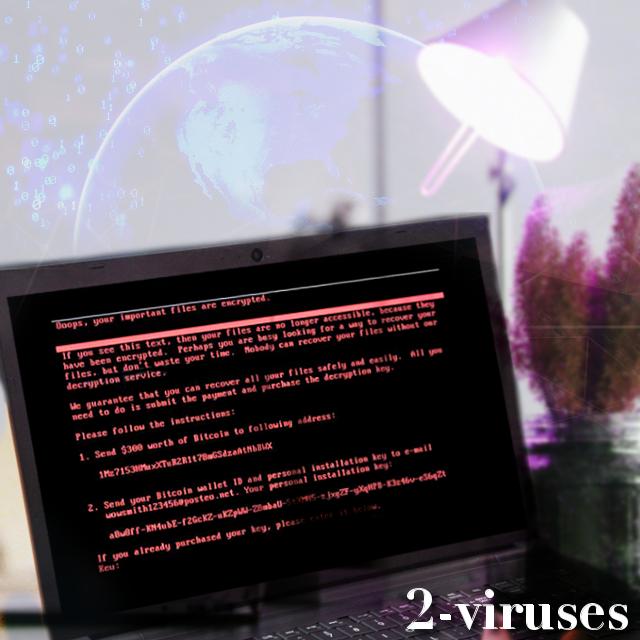
While very little time has passed since WannaCry caught everyone by the throat and forced to tremble before its feet, now we have to discuss a similarly-terrible situation. We first encountered Petya (or NotPetya and Petna) crypto-virus back in March of 2016 and its distribution was not evaluated as highly prevalent. Yesterday, security researchers were disturbed by multiple reports from different countries, suggesting that a frightening ransomware infection has managed to inflict its encryption on a bunch of innocent computer-owners. Companies indicated that their operated devices displayed a frightening messages, urging them to pay if they ever wish to restore their files back to normal.
We were wondering: did you do your homework and back up your files? Similar accidents can become more and more frequent, making the creation of alternative sources of files a crucial action. That is, if you do not intend to make hackers richer by sending them $300 dollars (this is the sum that Petya demands).
While the scope of victims that WannaCry infected might have been more massive, the amount of people, suffering from Petya’s terror, is dramatic enough. Malware has been considered to emerge in Spain, Denmark, India, United Kingdom and a whole bouquet of other countries, but Ukraine grabs the gold by being the leading-victim.
The activity of this variant has been extremely high in the latter country, bringing disruption even to government organizations that are no longer allowed to access their systems. Astonishingly, the variant blocked usage of ATMs and such seemingly irrelevant facilities like supermarkets. Right beside Ukraine (ironically) stands Russia and shares its pain from the fearsome crypto-virus.
While there had been a lot of confusion about where did the infection come from, security researchers have figured out the truth. Behind the recent Petya attack stands an unidentified hackers that managed to taint M.E.Doc. The latter service is a prevailing accounting software. You could guess who exploits this facility the most – Ukraine, the same country which has been determined to be suffering the most from Petya. Researchers examined the attack and decided that the culprit hijacked servers of M.E.Doc and managed to taint an update (which was later on distributed as a legitimate patch).
In a couple of hours or less, the downloaded malicious update will restart a computer. However, for the encoding to occur as planned, users will have to allow a CHKDSK process to be completed. This is the message that gets displayed during the artificial reboot of an infected device. If users are clever, they will be able to prevent ransomware from encrypting their files by shutting down their device entirely.
Petya crypto-virus should definitely terrify users as its encryption is done extremely professionally, which means that researchers will have a difficult time finding a decryptor. Therefore, we have decided to help users avert the infection in the first place by providing helpful instructions on how an operating system can be secured from this sample. You are vert advised to implement these steps!
Stop acting irresponsible and back up your valuable digital files as soon as possible. It is impossible to predict which ransomware infection will start leading the herd after Petya, but we do hope that you are prepared for a similar incident.
Source: wired.co.uk


