There is no way of stopping some cyber attacks from happening. A grand spam campaign, delivering payloads of Locky virus, is the focus of this article. The incident took place on the 28th of August and hackers are accused of sending 23 million of deceptive letters. Researchers from AppRiver revealed this discovery in their blog entry and even provided examples on how the infectious messages looked. All misleading messages were sent in 24 hours time. The number of possible victims is unknown.
Some background about Locky ransomware
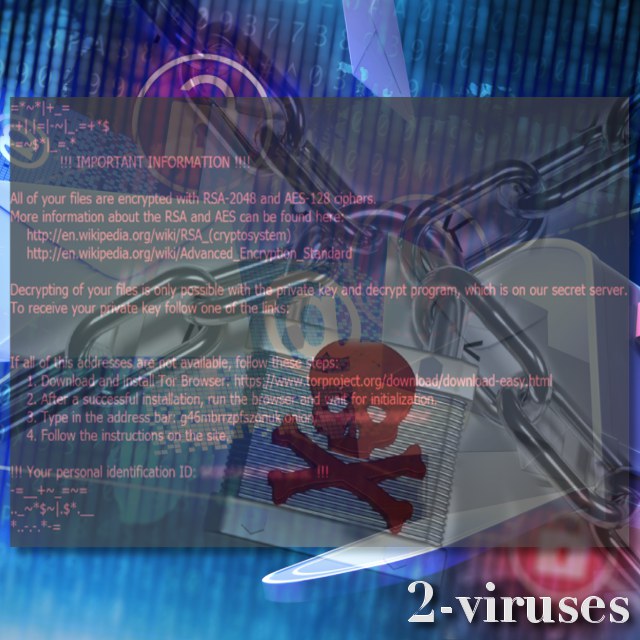
Even though Locky has been assumed to be many things (the most frightening ransomware infection and, at one time, a crypto-virus that was believed to be extinct), it still proves its status of a disturbing malware virus. This ransomware has been active for two years and over this time, we have announced multiple news on it. For instance, at one time, it was detected to use Facebook Messenger for distribution. Additionally, Trojan Fareit had also played part in the transmission process.
The recent spam campaign explained
According to the reports of AppRiver researchers, they indicate that misleading letters featured brief titles and barely had any texts inside. However, they did contain .ZIP attachments that, if downloaded, would have delivered Locky virus. By looking at the malicious messages that were sent around, we would hope that people were able to recognize these messages as completely unreliable.
Malicious .zip attachments hid additional VBS files which were meant to contact Greateshits(.)mygoldmusic(.)com websites. This domain was supposed to download the newest version of Locky: Lukitus ransomware that appends .lukitus extension to encoded data. This variant is one of the most recent Locky samples.
This and similar spam campaigns should remind you why looking through your email account is supposed to be done cautiously. Do not download attachments from unknown senders, especially the ones that transmit brief, illogical, irrelevant messages. Also, hackers usually make many typos or grammatical mistakes.
To make yourself immune to ransomware infections, back up your data in storages or USB flash drives. This action is recommended by many security researchers, and we do not miss a chance to remind of it as well. If you decide to back up your data, it is clear that not a single ransomware infection will have a chance. Since you will have alternative locations for your files, hackers won’t have leverage they need to demand a ransom. The distributed spam campaign brings Lukitus, a variant that requires 0.46 BTC (currently 2216.86 US Dollars) as a fee for decryption.
Source: blog.appriver.com.


